Why Legacy Legal Systems Increase Compliance Complexity for Law Firms

There is a question worth pausing on before getting into the detail.
When did your firm last assess whether its core practice management or billing systems still align with today’s compliance expectations? Not the standards from a decade ago, but the ones regulators, data protection authorities, and clients are actively enforcing now.
For many law firms, that review has not happened recently, and that is understandable. Running a practice is demanding, and systems that continue to function day to day rarely signal a need for change.
At the same time, the gap between current compliance requirements and what older systems were designed to support has grown. It is in that gap where complexity begins to build, often quietly over time.
This is not a technology article. It is a compliance-focused discussion with technology at its core. Understanding how legacy systems contribute to that complexity is the first step toward addressing it in a structured, confident way.
The Gap Between What Compliance Requires and What Older Systems Can Deliver
Many law firms still rely on practice management and billing systems that have not been significantly updated in years.
When these systems were first implemented, compliance expectations were defined and workable. Firms needed to run conflict checks, protect client confidentiality, handle client money correctly, and maintain proper records. The software built for this purpose performed well, and there was little reason to question it.
The nature of compliance has since changed, and it has changed considerably.
Requirements are no longer limited to internal controls. They now extend to how data is collected, stored, accessed, and shared across jurisdictions, and several significant obligations have been introduced over the past decade that older systems were never designed to address.
- The introduction of GDPR brought with it data subject rights, strict rules on the lawful basis for processing personal data, and a requirement to notify regulators of certain breaches within 72 hours, none of which a billing or matter management platform from an earlier era was built to support
- US state privacy laws added overlapping obligations for firms working with American clients, with more states continuing to legislate
- Anti-money laundering regulations expanded due diligence requirements at the start of every matter, covering a wider range of legal services than before
- Corporate clients and financial institutions now include security and compliance reviews as a standard part of how they select and retain legal service providers
Each of these developments added a new layer of expectation, and the cumulative effect is what creates genuine complexity for firms running older infrastructure.
What makes this difficult is not any single regulation in isolation. It is the way they have accumulated over time, each one assuming a level of data visibility and system capability that legacy platforms were not built to provide.
Most legacy systems were designed for record keeping and operational efficiency, not for continuous compliance monitoring or cross-system visibility, and that distinction matters more today than it ever has.
On one side, compliance now requires structured controls, traceability, and documented evidence at every stage. On the other hand, older systems continue to operate within the narrower scope they were originally designed for.
The result is a growing disconnect between what firms need to demonstrate and what their systems are equipped to support, and the timeline below shows how steadily that gap has widened.

Sources: Regulatory dates: GDPR, Official Journal of the EU (Regulation EU 2016/679), US state law dates: CCPA enacted legislation, California, Cyberattack figure: US Legal Support, Data Privacy Trends in 2025.
Five Areas Where Older Systems Create Compliance Complexity
The challenges do not always announce themselves. They tend to appear in the gap between what a system was built to do and what compliance now expects it to handle.
You can usually see that gap in a few familiar places.
1. Data is spread across systems with no single source of truth
Under GDPR and similar regulations, firms must be able to confirm what personal data they hold, where it is stored, and how long it is retained. That sounds straightforward until you look at where client data actually lives in a typical firm.
- A billing platform holding time and matter records
- A shared network drive with documents and correspondence
- An archived email environment that predates current systems
- One or more legacy platforms that were migrated but never fully retired
When a Subject Access Request arrives, or a regulatory audit is initiated, the absence of a central data register turns a routine obligation into an operational challenge. There is no quick resolution when data is fragmented across systems that were never designed to work together.
For a closer look at how these data gaps show up in practice and how firms are addressing them, read blog: 7 Data Issues Law Firms Don’t See Until It’s Too Late (And How to Fix Them)
2. Conflicts checks that work until they do not
A reliable conflicts check requires real-time access to every active and historical client relationship across the firm. It must include lateral hires and their prior client histories, related parties, and matter-specific considerations.
Legacy practice management systems, particularly those built on siloed databases, were not designed for that level of visibility.
The issue rarely appears at the start. It tends to surface after engagement letters are signed, or later, in a professional indemnity claim once the matter has closed. By the time it becomes visible, the risk has already materialized.
3. Access controls that fall short of current security standards
Frameworks such as ISO 27001 and SOC 2, which clients increasingly reference in due diligence questionnaires, require role-based access control, multi-factor authentication, and detailed audit logging.
Legacy systems were not designed with these requirements in mind. In practice, this often leads to environments where access and control mechanisms are less structured than current standards expect.
Firms may find themselves operating with:
- Broad user permissions that have not been reviewed in years
- Shared administrative credentials that limit clear accountability
- Manual overrides that are not consistently logged or traceable
These patterns are not always intentional. They develop over time as systems are extended, integrated, or worked around to meet evolving needs.
4. Every regulatory change becomes an internal project
In a modern platform, regulatory updates are handled through structured system changes with clear documentation and audit trails.
In a legacy environment, the process is different. The firm first assesses whether the system can support the change. If it cannot, a workaround is created. That workaround is then communicated to fee earners, and the firm depends on individuals to follow a process that the system does not enforce.
The result is a compliance model built on behaviour rather than system design. This is exactly what regulators examine when assessing whether a firm has adequate controls in place.
5. Billing errors that build up without detection
Accurate billing is no longer only a client service issue. It is also a compliance requirement. Proper time recording, correct disbursement coding, and the absence of duplicate entries all require demonstrable controls.
Legacy billing systems provide limited exception reporting and no automated anomaly detection. Errors build up without being identified and typically surface in one of three ways:
- A client audit that reveals discrepancies
- A fee dispute that exposes inconsistencies
- A professional conduct investigation in more serious cases
The issue is not individual error. It is that the system provides no mechanism to detect or prevent it. That distinction matters when a firm needs to demonstrate adequate controls.
The Invisible Cost of Leaving Things as They Are
One of the reasons this issue persists is that the cost does not arrive as a single visible expense. It builds gradually, often appearing as isolated incidents rather than a connected pattern.
Time written off while reconciling records that do not align. A compliance consultant brought in after a regulatory enquiry.
A fee earner spending longer than necessary on tasks better tools would handle in minutes.
A prospective client asking a security question the firm cannot answer with confidence.
Individually, none of these feel like a system issue in the moment. Taken together, they point to something structural.
The real impact becomes clearer when a formal enforcement action occurs. The cost rarely ends with a penalty. It extends into remediation work, external advisory support, internal process changes, and the management time required to respond. These are costs firms often underestimate until they are already in motion.
At the same time, the legal technology market continues to grow. Multiple independent forecasts place the global legal technology market at a CAGR of between 9% and 10% through to the early 2030s, driven in significant part by rising compliance and risk management demands. Investment in this space is not slowing down.
Firms that delay modernisation are not maintaining the status quo. They are operating with growing constraints while expectations continue to rise around them. In a profession where regulatory standing and client trust are foundational, that gap creates avoidable pressure over time.
What Actually Fixing This Looks Like
There is a meaningful distinction between patching a legacy system and building a compliance infrastructure.
Patching a system buys time. It may get you through another renewal cycle or audit, but it does not address the underlying risk. Building a compliance infrastructure means working at the root level. It involves unified data governance, reliable conflicts and intake processes, structured access control, and billing systems that can detect issues as they occur.
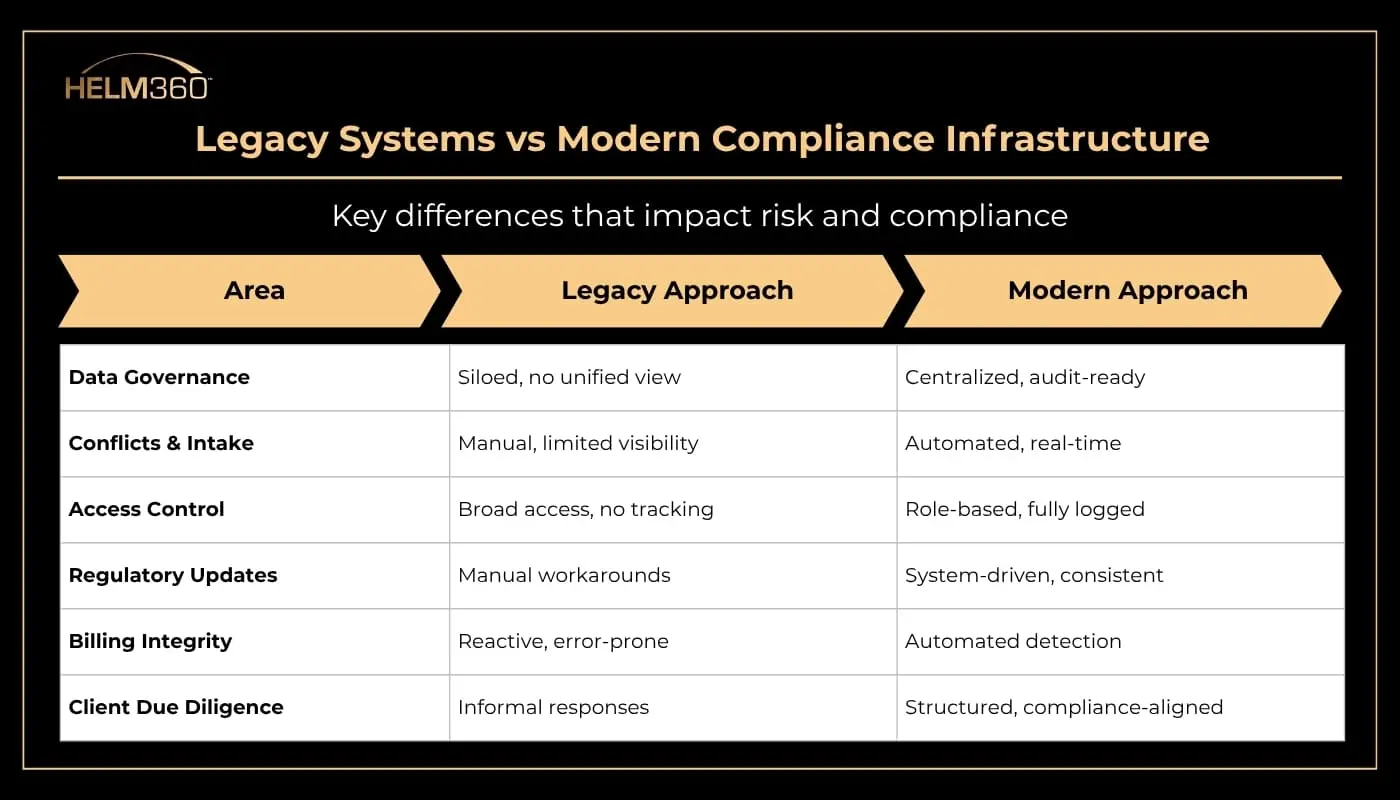
This shift becomes clearer when you compare how legacy and modern environments operate:
For most firms, this does not mean a single disruptive overhaul.
It starts with a structured assessment: understanding where the gaps actually are, which ones carry the highest regulatory exposure, and what a phased plan to address them looks like in practice.
The starting point is almost always data. Knowing what your firm holds, where it is stored, and who can access it creates the clarity that everything else builds on.
This is the work that Helm360’s Risk and Compliance practice is built around. Not as a vendor offering a standard replacement, but as practitioners who have spent over a decade working inside law firm operations. That work spans Elite 3E upgrades and migrations, implementation of the full Intapp Risk and Compliance suite as an official Intapp services partner, GRC framework design, and data governance projects that produce audit-ready answers rather than manual searches through archived systems.
Helm360 also holds SOC 2 certification and ISO 27001 accreditation. For firms navigating increasing client due diligence on their technology supply chain, that matters. Working with a certified partner means the infrastructure supporting your practice already meets standards that clients and regulators increasingly expect to see documented.
Closing Thought
Most firms are not in this position because they ignored compliance. They are here because the systems they invested in were the right choice at the time, and replacing something that continues to function in practice is never a straightforward decision.
But the compliance expectations around those systems have continued to grow. And at a certain point, the effort required to work around what a system cannot do starts to cost more than addressing the gap directly.
If your firm is at that point, or approaching it, the most useful next step is a clear-eyed look at where things actually stand. Not a technology project, just an honest conversation about what the current setup can and cannot support.
That is exactly where a conversation with the Helm360 team tends to start, and it is the right place to begin.


